Introduction
The fault tree analysis, also known as FTA, is a model used to understand how systems or processes fail. Furthermore, it helps with identifying the best way to reduce risk and to determine the probability of an event occurring. The FTA shares many of the same aspects as the BowTie Analysis (BTA). The model was originally made by H.A. Watson working at Bell Laboratories with the goal of evaluating ballistic missiles. Since then, the FTA has spread to a wide range of industries where identifying risks and calculating probability is relevant.
The Model
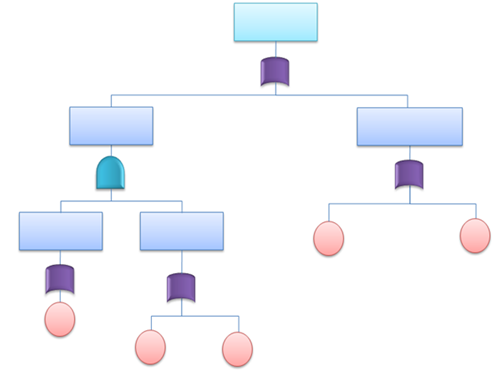
The model usually consists of 4 elements:
The main event: The event at the top of the model which shows what is being analyzed within the fault tree.
Intermediate events:Events that occur between the basic events and the main event.
Basic events: A failure or error which results in another event happening. These are shown as circles on the bottom of the model
AND/OR gates: These are the link between the events in the fault tree. AND gates are symbolized with a flat bottom and means that all of the underlying basic events have to happen in order to trigger the intermediate event above. OR gates are symbolized with a curved bottom and means that just one of the underlying basic events have to happen to trigger the intermediate event above.
How can we use this in our projects?
A single fault tree is used to analyze and understand a single event, therefore we need to have conducted a risk analysis of the project before an FTA becomes relevant. Once we have the risk analysis we use the FTA's on each of the hazards we have identified. It basically comes down to the following five steps:
1: Define the undesired event to study
2: Obtain an understanding of the event
3: Construct the fault tree
4: Evaluate the fault tree
5: Control the identified hazards
By following these steps you can reduce the risk within your project and at the same time determine which risks you are already protected towards and which risks you need to put more ressources into.








